Unravelling a Mimikatz campaign
This is a short blog analyzing some artifacts left over by a Mimikatz operator's campaign.
Background
While doing to some internet dumpster-diving (as I like to call it) I came across an open directory belonging to a threat actor's Mimikatz staging server (see Figure 1). The threat actor's server was hosted on DigitalOcean AS14061 (165[.]232[.]*.*) and a takedown request was submitted by myself to the DigitalOcean Abuse team.
Figure 1: Mimikatz opendir
The files on the server were not that interesting, most of it was default Mimikatz components from the GitHub and other resources online. The files are available on VirusTotal too if needed.
- im.ps1 (Invoke-Mimikatz PowerShell script)
- https://www.virustotal.com/gui/file/1b441fde04d361a6fd7fbd83e969014622453c263107ce2bed87ad0bff7cf13f
- mimidrv.sys (signed Windows Driver Model (WDM) kernel mode software driver)
- https://www.virustotal.com/gui/file/f9b01406864ab081aa77eef4ad15cb2dd2f830d1ef54f52622a59ff1aeb05ba5
- mimikatz.exe and mmktz.exe (default OS credential dumping tool that targets LSASS.exe in Windows)
- https://www.virustotal.com/gui/file/92804faaab2175dc501d73e814663058c78c0a042675a8937266357bcfb96c50
- mimilib.dll (DLL for Injecting into Windows Security Support Providers)
- https://www.virustotal.com/gui/file/7ffce7f6d7262f214d78e6b7fd8d07119835cba4b04ce334260665d7c8fb369a
- rx.php
- Unavailable - potentially Reactive Extensions for PHP
- test.txt
- zero byte file
The reputation of the staging IPv4 address was clean (zero detections) across OSINT sources at the time of writing. This includes AbuseIPDB, VirusTotal, GreyNoise, and spam blocklists, among others. Therefore, it's likely this is a new campaign.
Pulling on the threads
Interestingly, the staging server (where they hosted the payloads) also contained a list of 78 files, at the time of writing, with the following naming convention: “<IPv4 address>_<date>_<time>.creds” (see Figure 2). Most of this blog will focus on analyzing this victim data to try to understand the scope of the campaign and learn more about the threat actor.
Figure 2: Empty ".creds" files on the opendir DigitalOcean host
By extracting and analyzing the data from the file names of the 78 ".creds" files it was possible to create a clearer picture and pattern of activity by this threat actor. The key findings were as follows:
- The threat actor was active between 22 July and 7 August 2022 (see Figure 3)
- There were 78 attacks in total, based on number of files created in the open directory
- 54 unique IPs were targeted, the vast majority of which were located in Japan, followed by the US, Canada, Ireland, Ukraine, Russia, India, and Australia (see Figure 4)
- 44 unique IPs were from fixed line IPs on Maxihost Japan (see Figure 5)
- Several IPs from the same CIDR range were targeted multiple times on different days
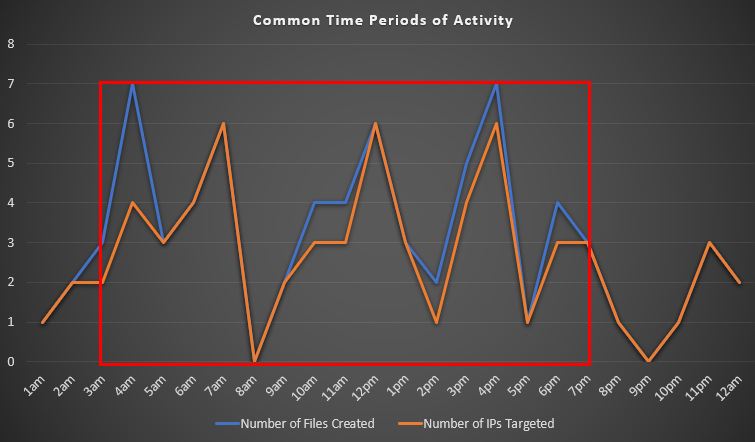
- Attacks began mostly around 4am (UTC) and ended most days around 7pm (UTC) (see Figure 6)
Figure 6: Time of activities performed by the Mimikatz operator
Assessments based on analysis of the data available: