Background
Active since at least August 2021, a new English-speaking threat actor calling themselves "1977" has developed and advertised a new eCrime market on multiple underground forums called Darth Maul Shop. This blog aims to highlight some of the key aspects of a new emerging eCrime market, analyze its reception by other threat actors, and discuss the underground cybercrime communities making money buying and selling credentials without launching any intrusions themselves.
If you want to learn more about Initial Access Brokers (IABs), SentinelOne recently shared a good up-to-date overview of this type of threat actor and how they interface with various ransomware groups and the types of services they offer. These IABs can be just as dangerous as the ransomware groups themselves, as they are capable of infiltrating a target network and achieving the privileges of "Domain Admin (DA) access with reach to over 10,000 hosts."
The eCrime market has also shifted recently with the arrival of a new and improved Genesis market, which has been active since 2017 and is one of the largest of the underground economy alongside RussianMarket, 2EasyShop, and xLeet. Sophos researchers recently covered how Genesis sells stolen credentials, cookies, and digital fingerprints that are gathered from compromised systems, providing not just the data itself but well-maintained tools to facilitate its use.
Darth Maul (aka 1977.SH) eCrime Market
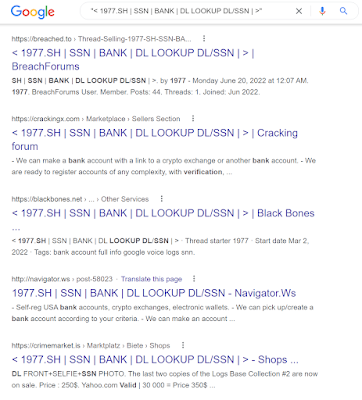
The interesting thing about Darth Maul shop is there are very little mentions of it across the usual OSINT sources, despite existing for around one year. A cursory search across some of the eCrime forums, paired with a little Google dorking, revealed over a dozen accounts for the admin of Darth Maul market.
Figure 1: Google Dork for 1977 aka Darth Maul
The admin, who goes by "1977" (aka "1977ko", “000x0”, or “darth1977maul”), has been active on these forums since around February 2022. One thing that stands out about the admin's forum activities is that they rarely interact with other forum members outside of their own threads. This is purely a marketing campaign instead of looking to make connections or build relationships with the forums they advertise on.Figure 2: Forum account profiles of Darth Maul admin
The new market (Darth-Maul[.]top) has been around for about one year according to WHOIS data (it also uses 1977[.]sh as a mirror). The registrant org is called "Hakintoshionio", apparently based in Kazakhstan, and has "afakjbfkhbjqkbwe1@hotmail.com" as the tech contact email. The admin has also created a Telegram channel that has over 2,300 users at the time of writing.Figure 3: Telegram channel and Whois Record
The advertisements of the Darth Maul market highlight some of the main items that are purportedly for sale on the site. In order to compete with some of the other eCrime markets, the admin has created attractive posters to catch the attention of other forum members. This type of marketing is often used cybercriminal services, one that always stood out was the Cerberus Android Malware-as-a-Service (MaaS) platform, which used similar attractive graphics and banners on various Russian-speaking forums.
Figure 4: Items allegedly for sale on Darth Maul market (March 2022)
Figure 5: Additional items advertised on Darth Maul market (May 2022)
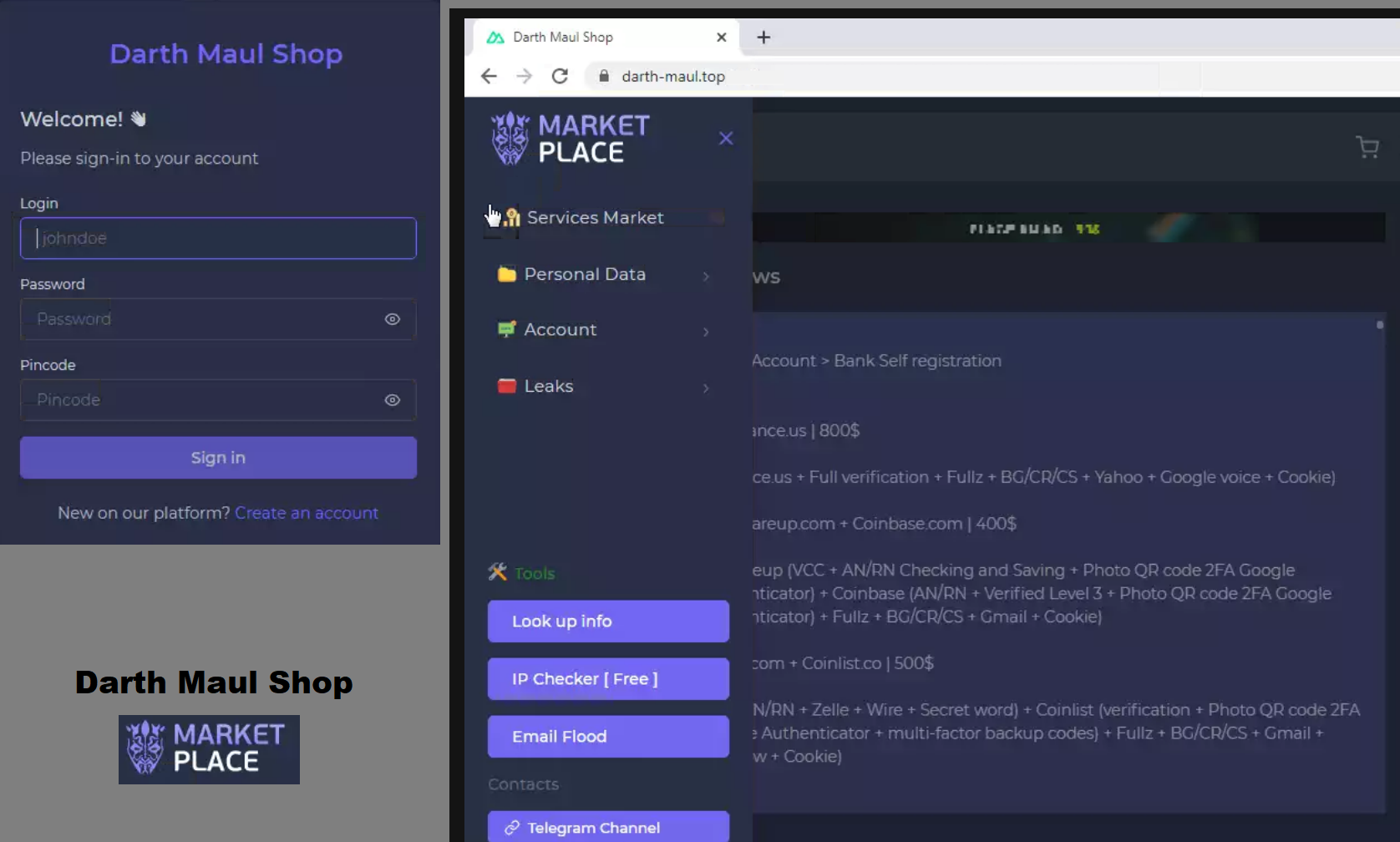
The Darth Maul Shop itself honestly looks like it was designed by someone straight out of college and appears to be still in the early stages of development. However, some of the things for sale (or claimed to be for sale) are interesting and worth covering.
Figure 6: Darth Maul eCrime market (August 2022)
Another post on the forums, where "1977" advertises the market, highlights the rules for the market members, which were last updated in May 2022. These are fairly normal for underground markets that offer a platform for buying and selling credentials and other stolen digital goods.
Figure 7: Site rules for Darth Maul market
Like other eCrime markets selling data and credentials, Darth Maul market permits other threat actors to sell their items and use the site as a digital middleman for buyers and sellers.
Figure 8: Darth Maul market
The presence of a user called KapustaWorld (although unconfirmed if it actually is them) on the Darth Maul market is also notable and also potentially shows that the market is gaining traction among established cybercriminals. Rivals on other Underground Forums
The basis of this blog actually began because a 106.42MB file called "darth-maul_shop_logs.txt" was uploaded to VirusTotal on 13 May 2022 containing what appears to be (unconfirmed) all the scraped logs stored in the site.
Further research into the TXT file, uncovered that the Darth Maul market got off to a bit of a rocky start. Back in February 2022 when the market was trying to attract new users, some members on the infamous Breached[.]co forum leaked the entire collection of logs from the site for anyone to download from anonymous file-sharing Cloud services, such as Mega[.]nz and Anonfiles[.]com. Looks like there really is no honor among thieves.
Figure 9: Darth Maul market logs dumped to Breached[.]co
This is a hugely embarrassing event for the Darth Maul market admin "1977" who will now been by other cybercriminals as an incompetent threat actor who cannot secure the data of their market's users. The market is seemingly struggling to grow as a result. Analysis
At Black Hat USA 2022, former director of CISA, Chris Krebs, said he believes that we as a cybersecurity community have "over-fetishized the APT threat. We’ve over-rotated on the SVR and MSS while cybercriminals have been eating our lunch in the meantime". This aligns with the fact that there is a staggering number of stolen credentials fuelling various eCrime markets that have been an often ignored, but persistent threat for years.
The threat of eCrime markets was especially demonstrated by the LAPSUS$ cybercrime group from late 2021 to early 2022, who managed to gain access to some of the top technology firms in the world, such as Microsoft, Vodafone, Samsung, Nvidia, Okta, and Globant - who you'd think are some of the organizations spending the most of cybersecurity in the world - using credentials and cookies available via the underground, similar to Darth Maul market.
The future of Darth Maul market and "1977" remains to be seen and looks bleak due to the data dump. But one thing is for sure, launching your own cybercrime has become more accessible than ever before and organizations need to wake up to this threat before it is too late.
Obligatory Phantom Menace gif