Raspberry Robin: A global USB malware campaign providing access to ransomware operators
In fact, the list of blogs I do recommend to read to catch up on this threat are as follows:
- https://redcanary.com/blog/raspberry-robin
- https://www.microsoft.com/en-us/security/blog/2022/10/27/raspberry-robin-worm-part-of-larger-ecosystem-facilitating-pre-ransomware-activity
- https://blog.sekoia.io/raspberry-robins-botnet-second-life/
- https://decoded.avast.io/janvojtesek/raspberry-robins-roshtyak-a-little-lesson-in-trickery/
- https://research.checkpoint.com/2023/raspberry-robin-anti-evasion-how-to-exploit-analysis/
- https://securityintelligence.com/posts/raspberry-robin-worm-dridex-malware/
- https://blogs.cisco.com/security/raspberry-robin-highly-evasive-worm-spreads-over-external-disks
- https://www.cybereason.com/blog/threat-alert-raspberry-robin-worm-abuses-windows-installer-and-qnap-devices
What's so special about RaspberryRobin?
"What should I care? It's just another USB malware right?" Wrong... it leads to ransomware.
This USB malware is not like your usual VBS self-copying low grade stuff, it is more like the BadUSB campaigns from a few years ago that was reportedly linked to FIN7 and led to BlackMatter or REvil ransomare. Microsoft's report on Raspberry Robin was the first to reveal that RaspberryRobin is also leading to multiple other top-tier malware loaders such as SocGholish, IcedID, Bumblebee, and Truebot, which are all well-known ransomware precursor families.
Raspberry Robin has shown itself to be an emerging player in the big game hunting ransomware ecosystem. USB malware has proven to be an old, yet still effective method to establish an initial foothold inside target environments.
But how does it spread?
Details about how the Raspberry Robin malware actually gets on to the USBs are a little hazy, but the malware has virally spread. In October 2022, Microsoft reported "that nearly 3,000 devices in almost 1,000 organizations" saw "at least one Raspberry Robin payload-related alert in the last 30 days."
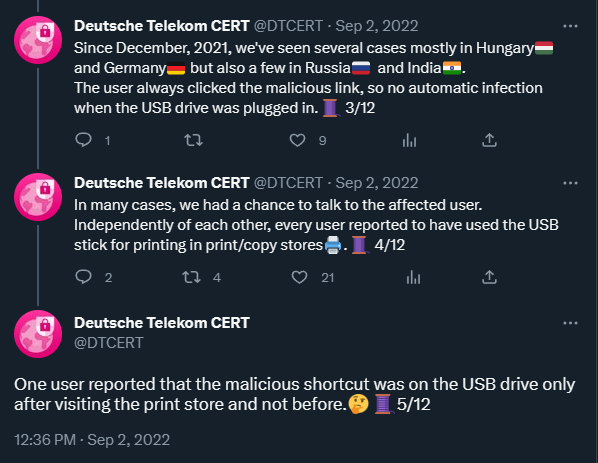
In September 2022, Deutsche Telekom CERT tweeted about how they observed the malware in Hungary, Germany, Russia, and India. All these Raspberry Robin cases involved a user clicking on a malicious shortcut (LNK) file when the USB was plugged in. Most interestingly, Deutsche Telekom CERT found that all the affected users reported to "have used the USB stick for printing in print/copy stores". This was a fairly strong indication that something has happened to these printers at the print/copy stores that ended up with them potentially being one of the main sources of USB infecting malware, at different countries around the world.
We got some further clarification from Microsoft, when they identified a previously undisclosed .NET spreader DLL that was responsible for creating the Raspberry Robin LNK files on external USB drives. This .NET spreader DLL was also distributed by another related and previously undisclosed malware family dubbed Fauppod.
Microsoft, however, did not mention the usage of printers or print/copy stores to aid distribution of the USB malware. Others in the CTI community though, particularly those in CuratedIntel, did share with me that they also observed printers being the source of infected USBs as well, which is in line with Deutsche Telekom CERT's findings. Some researchers speculate that the Raspberry Robin operators may have targeted vulnerable printers exposed on the Internet (as there's not shortage of those) or perhaps there was some unreported supply chain attack. The full extent of how these printers are getting infected and spreading the Raspberry Robin LNK files is still yet to be revealed.
Detection Opportunities: Infection Chain
The full infection chain of Raspberry Robin has been explained well many vendors over the last year and it has not changed much since it first emerged. The reports mentioned above, particularly by Cisco and Cybereason, as well as the original RedCanary blog, are all worth making notes from to detect and stop this threat.
From reading all these reports, I found that the most simple way to detect Raspberry Robin using Splunk SPL log searching rules specifically was the following:
- 1) FileName=cmd.exe AND LinkName IN ("*D:\\USB*", ".lnk")
- 2) CommandLine=msiexec AND CommandLine=*:8080*
Detection Opportunities: The Botnet
The C2 network is made up of compromised Internet-of-Things (IoT) devices, namely network attached storage (NAS) systems with hijacked DNS settings. The majority of Raspberry Robin C2 servers are QNAP or Acrobox systems exposed to the internet. The image below is a common sight when you're investigating Raspberry Robin. These are some IOCs I came across earlier in April 2023 and also tweeted.
Indicators of Compromise
For my threat research with the Equinix Threat Analysis Center (ETAC), I did my own investigation into Raspberry Robin USB malware submissions to VirusTotal using the YARA Live Hunt feature. I created a simple YARA rule (available below via a GitHub Gist) using all the C2 domains I could find related to Raspberry Robin, which was around 270. Then any time a user submitted a sample to VirusTotal with any of the C2 domains embedded, I would get an email alert. Doing this all through April 2023, it uncovered all the samples of Raspberry Robin listed on the table below.
By checking the submitter IDs and countries where the samples were uploaded from, I could then create the map that is the title image of this blog. In less than one month, the USB malware was detected around the world, from APAC, to EMEA, to AMER. A truly global malware campaign to keep an eye on.
| First Seen | Indicator - SHA256 | FileName | Embedded Domain |
|---|---|---|---|
| 1-May-23 | 8cc69700d007da11ee29a37d9accd87be1e9b16c49e8d8015b4cc237de803e24 | q0[.]wf | |
| 30-Apr-23 | de62ea5d304259d153101e488449afb51f536a2c65082f929d298939de129355 | ag.a | m0[.]yt |
| 30-Apr-23 | 1c8b93c05c58886a9edbf2818a2cc6bcc06f003b8919f76f7c0af6a9602bea35 | sq.jpg | 4aw[.]ro |
| 30-Apr-23 | 912553b71902cc38fe00b59c137b177b46851de18c19445d58110c77bf8ef2a3 | by.ffa | 0j[.]wf |
| 29-Apr-23 | 20f0c9fb11408d6bc2633aa9c453a10ff679974f9815d1fcd86f0e32afb9d8ca | j1n[.]me | |
| 28-Apr-23 | 82a9dcff810ad5c7d2e6877105e19b83da81f789a1d34c5a496757770b5f3fdd | 3h[.]wf | |
| 28-Apr-23 | 2775df615c2afade82072bdb28550009edbdf3c5823bcf555f140b5148c7a449 | frddq.ico | 5g7[.]at |
| 27-Apr-23 | cfaca73578c02db9745981e10530552842e27b784de51698816436a2196b4117 | osz.nd | fnx[.]wf |
| 27-Apr-23 | cfb3c6f18f4b3da1f12fc1b8d465daa92dad5a5ecd478dd58b33366a5c0733a1 | aqgvw.ico | vs[.]gy |
| 27-Apr-23 | 3fd2478c7b9f2c19bc3c4a16d09f68ff74594d7115ec0909a4a0f45e9f0e1624 | qjm.bmp | i0[.]wf |
| 27-Apr-23 | 27bfaeda1d7ee28552343a960255a73b5df69b607462d3c43bd1438b86343972 | 3z[.]nu | |
| 26-Apr-23 | e39500904172d1c47d74aef5b3dc063cce480a3ed1da2a0ae108049bd42ed3a7 | zfl.cfg | zjc[.]bz |
| 26-Apr-23 | 9f81327ecf7b0ed1ee26e247a6cb424a5773c110a8e590f9f70a18d25ae974ae | bzrsd.q | bcomb[.]net |
| 26-Apr-23 | 5ea3c6000a02790cf983e41729b77102e255bc8e4cc009722c09a17d56d5e253 | sggr.s | jzm[.]pw |
| 26-Apr-23 | 1004549b93d8bc1828c26647ed45a88c245cb5ebe1326dd496070c492e294d39 | vszkn.sav | 5g7[.]at |
| 25-Apr-23 | 1ebe7d09e26f07d272a64278e0ae8fc1ba6b512dcf41035b5ece54d43d3198e2 | wycz.lnk | w0[.]pm |
| 25-Apr-23 | 0a1c697e4d8bb227fe4c7f854a80e6c0dbda9f3e36c319339255bd05dc54844c | pcv.kqn | w0[.]pm |
| 25-Apr-23 | 29615895e321580dd4ee81072f13c64ec61465ca6fc26eb155b31404f7556193 | osz.nd | h0[.]pm |
| 25-Apr-23 | fce6cf771ff163d943938ff42e8863c143c817ebcbdfa4140b64c1a4d4133301 | xac.bmp | 4xq[.]nl |
| 24-Apr-23 | 4c0700588d9481b0bf6a554a08ec0698a71f8ca86b07cd727784db22669e1f4a | mwgq[.]net | |
| 24-Apr-23 | 71bb34d64d68e5f53edb2c31125ba4a3e41806c7bd254eb061c5985b06e937c6 | soxxg.png | 0j[.]wf |
| 24-Apr-23 | 7c6a000344c06ae53b82f7b28e0589cfb0bf3c1b5bec8db40eecba60f0d8d470 | phi.bmp | 5v0[.]nl |
| 22-Apr-23 | 183312f1f8c16fd308bf118eb4c6ef472a022d7d11b80f8ade7061cc4924c6ec | 3h[.]wf | |
| 22-Apr-23 | 10b0b4d885884394459031f989fa722366152a9e08189c61cf62543fb2368c04 | 4xq[.]nl | |
| 22-Apr-23 | 10a370e6d7c78b21cebc1261f01b38c1f866001ea0db3bc9962b0acd7aef1a59 | qjm.bmp | li1iv[.]com |
| 21-Apr-23 | ec1c8664d22bb000fd241dfee83719922ef06652bf882f7367b9c5471d96f71d | o7car[.]com | |
| 21-Apr-23 | 7575e400b71d1cb4609d1aeea977f6a2faa5f9bdc4b385581a2a9e47a5e7be34 | qjm.bmp | 4j[.]pm |
| 20-Apr-23 | 6268485f4f755d3dd6bc62de14837e5e8eb9d76ff9237da3e9c61f8b937cef26 | qjm.bmp | 6qo[.]at |
| 20-Apr-23 | 3472bf25ab439812521d186fae3de49b75ad7dd98972a69b4be345449056000a | ynyl.gt | q0[.]pm |
| 19-Apr-23 | e8c44a1f7188c6a685c2a81fcca6909ba5c13175bfc800a629d664f8a9580cc9 | qjm.chk | 6w[.]re |
| 19-Apr-23 | d26e14a8b41ecb99e9b3ed19a80d5034bd31f5ce678aa0ad9bd5927f94283ac2 | qlmhc.kll | 8t[.]pm |
| 19-Apr-23 | be72d3c6a59830cb29baf6d4b3eec230a55724b20f24e42d30087c26eef07b32 | petgz.zyn | qji6[.]com |
| 18-Apr-23 | dae94d3bbcbb661a50cad43cad488ac90e2a1e4643a338aedfb431e2a3b8eba0 | qjm.bmp | 5v0[.]nl |
| 18-Apr-23 | 744c2a1cd50555fdecd24fc03eb16286a4ceb2efd46c4b0291ae4808861883ca | xphfk.sav | 7d[.]rs |
| 18-Apr-23 | a26e6e9c2a804cad9bf392841e5e02beee3e58ccbb6bc3848cb0981cfab00ccb | gzqo.q | eznb[.]net |
Raspberry Robin C2 Domain YARA Rule