Brute Ratel cracked and shared across the Cybercriminal Underground
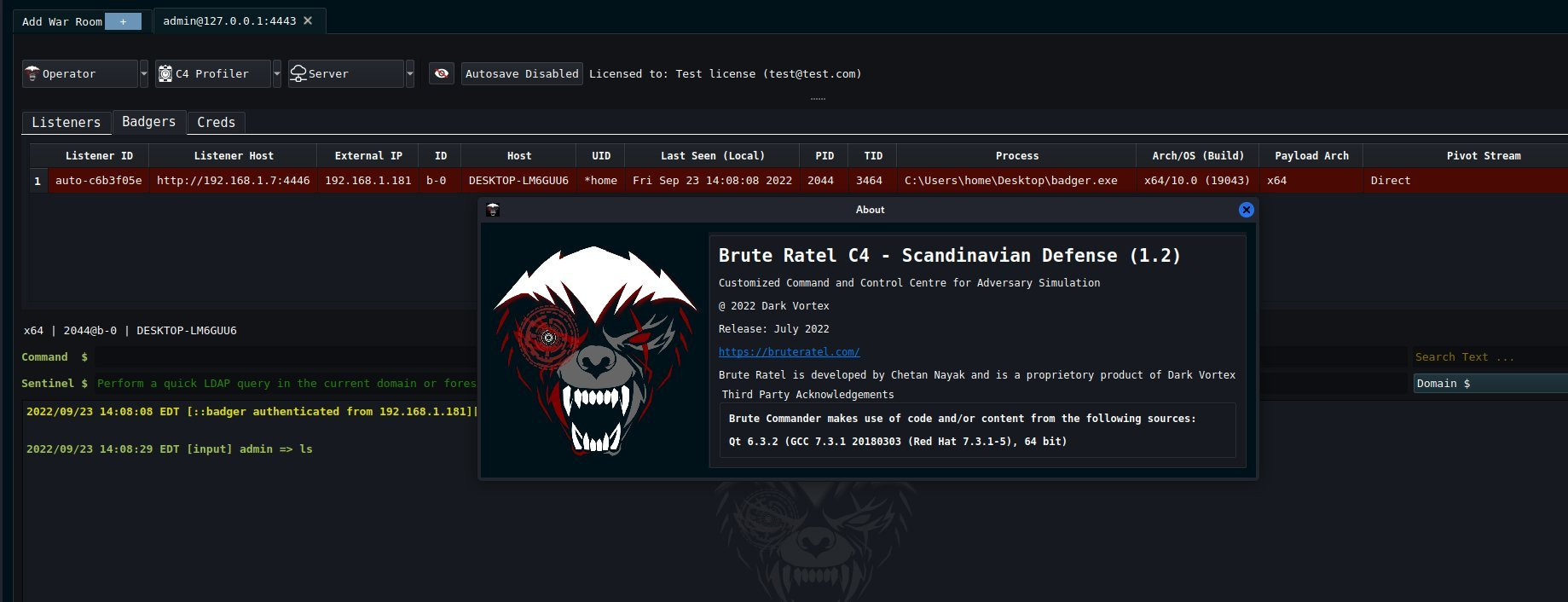
A short blog to document the proliferation of an advanced commercial penetration testing tool among cybercriminal threat actors across various Russian- and English-speaking underground forums. What? Available since December 2020, Brute Ratel C4 (aka BRC4) is one of the hottest new Red Team frameworks to hit the scene. It is similar to other frameworks such as Cobalt Strike but is uniquely concerning for its focus on evading endpoint detection and response (EDR) and antivirus (AV) tools. A technical analysis of BRC4 has already been provided by Palo Alto Networks Unit42 (see their blog here ). At 19:59:20 UTC o n 13 September 2022, an archive file called " bruteratel_1.2.2.Scandinavian_Defense.tar.gz " was uploaded to VirusTotal. This file contains a valid copy of BRC4 version 1.2.2/5. On 28 September, the developer of BRC4, Chetan Nayak, tweeted unfounded and disproven accusations that archive was leaked by MdSec and said they were the ones who ...