Tips for Investigating Cybercrime Infrastructure
I'm surprised this is my first blog of 2023, but I have been more busy than usual. My work at the Equinix Threat Analysis Center (ETAC) has been very engaging and when I'm not chasing cyber bad guys with ETAC I'm writing down how to do it as I'm developing SANS FOR589: Cybercrime Intelligence.
While researching packers and crypters (that are used to obfuscate malware code, like VMProtect or UPX), I came across a site in the search results billing itself as a generic "FUD Crypter" as-a-Service type offering (FUD = Fully Undetectable in cybercriminal lingo). The website "fudcrypter[.]io" is still online and looks pretty amateurish to me and was ripe for investigating.
I navigated around the site and hovered over some of the buttons and found redirects to another website called "data-encoder[.]com". This second site, however, was offline at the time I tried to visit it. But using a coveted CTI analyst tool I like to call the Wayback Machine I was able to see what it looked like.
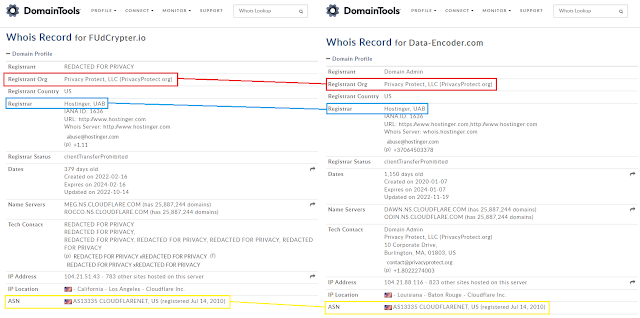
I then decided to compare the Whois information between the two sites and, sure enough, there was a similar pattern that I could use to deduce both were most likely created by the same threat actor due to several factors; namely: use of the same domain registration services and hiding behind the Cloudflare CDN (more on that later).
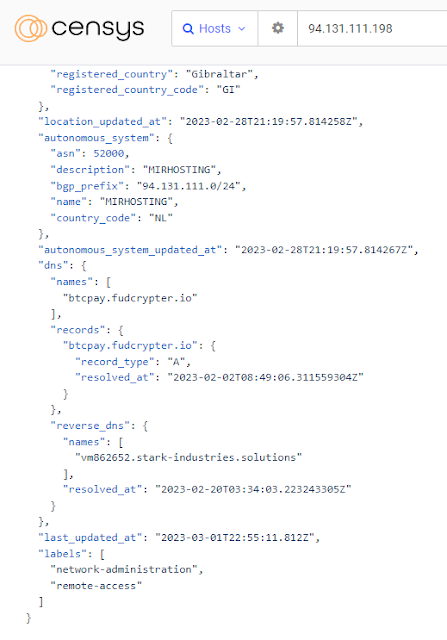
I wanted to find out more about FUDcrypter and Data-Encoder sites so I turned to some of my favourite Internet scanning services Shodan and Censys (two tools I believe any good CTI analyst should be well-acquainted with). I was not able to find much for data-encoder as the site had been down for a while it seems. But I did get lucky with the FUDcrypter site. I used Censys Search to find systems with the domain in the DNS settings.
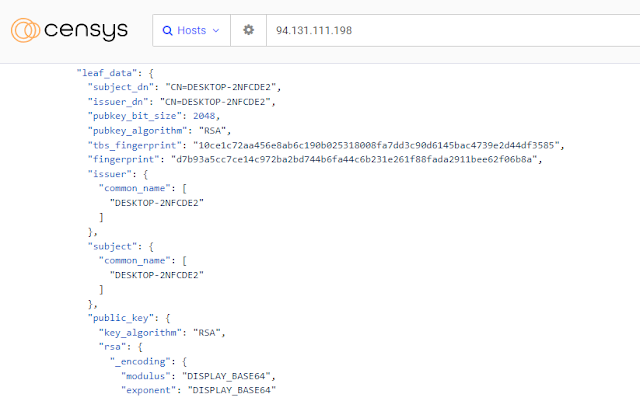
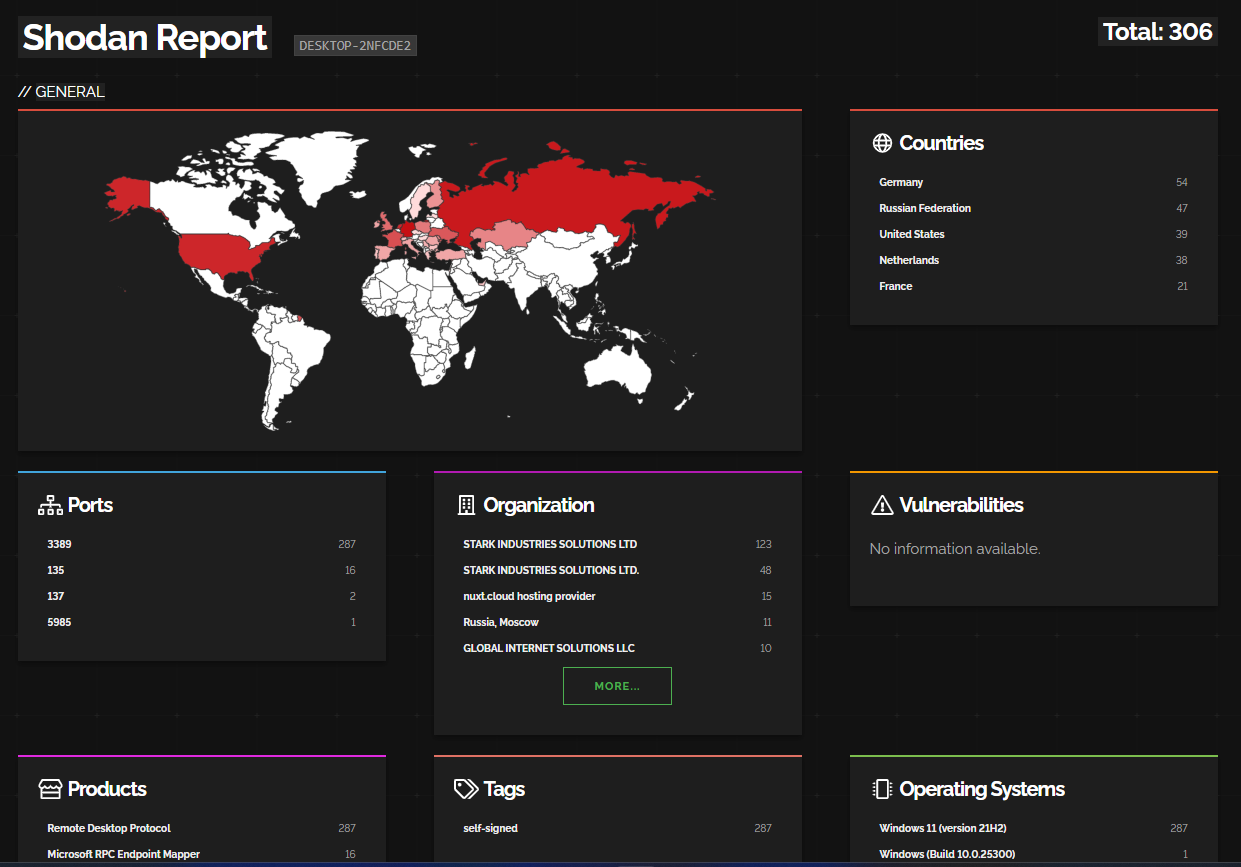
For bonus points, we can also pivot off of one of the other artifacts in the scan data. This includes the Windows Endpoint Hostname "DESKTOP-2NFCDE2" of the VPS used to host the site. It is possible to potentially identify other types of cybercriminal infrastructure potentially related to the same threat actor or related to the same service that is used by threat actors to host their malware C2s and other types of sites (like FUDcrypter).
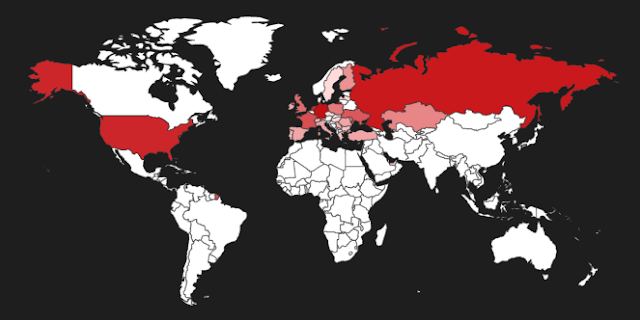
When I found the njRAT C2 server I looked at the VirusTotal relations of the IP and found an njRAT sample compiled in January 2023 called "Stub.exe". I did not confirm if it was packed with FUDcrypter/Data-Encoder, however, the service did have several mentions of a "private STUB" for "users wants to be particular [sic]". The private STUB service was allegedly updated every day and was unique for the cybercriminal who pays for it. Interestingly, it also came with a customer support ticketing system via email or Discord and the FUDcrypter operators even claimed they could connect to the customer's system using TeamViewer or AnyDesk remote monitoring and management (RMM) tools to provide them support.
In closing, this blog was fun to put together and I will admit that I wrote it on my laptop from my bed after an evening session with my local 2600 crew. Hopefully this will inspire other curious threat intel analysts who also enjoy snooping on cybercriminal infrastructure.
See you around, Netrunners
References
https://web.archive.org/web/20230228040437/https://fudcrypter.io/
https://web.archive.org/web/20210517004154/https://data-encoder.com/
https://search.censys.io/search?resource=hosts&sort=RELEVANCE&per_page=25&virtual_hosts=EXCLUDE&q=dns.names%3AFUdCrypter.io
https://search.censys.io/hosts/94.131.111.198
https://search.censys.io/hosts/94.131.111.198/data/json?resource=hosts&sort=RELEVANCE&per_page=25&virtual_hosts=EXCLUDE&q=dns.names%3AFUdCrypter.io&at_time=2023-03-02T09%3A03%3A44.136Z
https://www.shodan.io/search?query=DESKTOP-2NFCDE2
https://blog.cyble.com/2023/01/18/aurora-a-stealer-using-shapeshifting-tactics/
Indicators of Compromise (available inside the links)
https://urlscan.io/result/e3de1fbb-d146-49fd-a78e-5471b73d86f4/
https://urlscan.io/result/b9fe896e-b3ba-4142-bc9c-50dd699484a3/
https://twitter.com/1ZRR4H/status/1593377638504087553?s=20
https://www.virustotal.com/gui/ip-address/91.109.178.9